





Read More
B Tech in Cloud Technology and Information programme, at Assam down town University, deals with the latest advancement in the field of could computing and information security. With the rising threat of data breach, the demand for skilled professionals in the segment is growing and we intend to bridge this gap with a skilled workforce that can take up future industry challenges.
Year wise Course Details
Courses for this semester
Workshop practice provides the basic working knowledge of the production and properties of different materials used in the industry. It also explains the use of different tools, equipments, machinery and techniques of manufacturing, which ultimately facilitate shaping of these materials into various usable forms. This course will train the students into competent persons for such mechanical works .
Workshop practice is a very vast one and it provides the basic working knowledge of the production and properties of different materials used in the industry. It also explains the use of different tools, equipments, machinery and techniques of manufacturing, which ultimately facilitate shaping of these materials into various usable forms.
Courses for this semester
In this course students will learn the C programming language and its fundamental programming concepts.It includes simple C language applications and variables, data types, functions, control structures, pointers, strings, arrays and dynamic allocation principles.
This course will introduce basic problem solving using computer programming languages and basic organization of computers, C programming language, developing programming aptitude. It includes knowledge of basic programming environments.
This course supports exploration in careers related to the design, development, support, and management of hardware, software, multimedia, and systems integration services. Students will acquire knowledge and skills enabling them to succeed in a technology-driven society and career pathway. Learners apply reading, writing, computing, communication, and critical thinking throughout this project-based learning experience.
The objective of the Engineering Chemistry is to acquaint the students with the basic phenomenon/concepts of chemistry, the student face during course of their study in the industry and Engineering field. The student with the knowledge of the basic chemistry, will understand and explain scientifically the various chemistry related problems in the industry/engineering field. The student will able to understand the new developments and breakthroughs efficiently in engineering and technology. The introduction of the latest (R&D oriented) topics will make the engineering student upgraded with the new technologies
The topics in this course include: Sample spaces; probability, conditional probability and independence; Bayes' theorem; probability distributions; probability densities; algebra of expected values; descriptive statistics; inferences concerning means, variances, and proportions; curve fitting, the method of least squares and correlation. An introduction to quality control and reliability is also provided i this course.
The concepts developed in this course will aid in quantification of several concepts in chemistry that have been introduced at the 10+2 levels in schools. Technology is being increasingly based on the electronic, atomic and molecular level modifications. Quantum theory is more than 100 years old and to understand phenomena at nanometer levels, one has to base the description of all chemical processes at molecular levels.
All engineering activities (design/ manufacturing/ operation/ servicing) for any product from any discipline involve a team of people who communicate graphically. Hence, every engineer must have exposure and some competence in presenting ideas as pictures, and be able to unambiguously interpret drawing from others. This course will help develop basic visualization competency as well as ability to representing ideas on both paper and computer.
This course provides free hand drawing techniques for various kind of geometrical constructions. This course also includes scales and dimensioning techniques to draw various projections such as orthographic projections and isometric projections. Sectional views of geometrical solids also form a part of the course.
Courses for this semester
The student should be made to: Gives a view of computer system from user’s perspective.Types of instructions. Understand the basic structure and operation of digital computers Familiarize the students with the implementation of fixed-point and floating-point arithmetic operations. Computer architecture is the science and art of selecting and interconnecting hardware components to create a computer that meets functional, performance and cost goals. This course qualitatively and quantitatively examines computer design trade-offs, teaches the fundamentals of computer architecture and organization, including CPU, memory, registers, arithmetic unit, control unit, and input/output components. Topics include a reduced instruction set computer architectures (RISC), using the MIPS central processor as an example, the interface between assembly and high-level programming constructs and hardware, instruction and memory cache systems, performance evaluation, benchmarks, and use of the SPIM/WinDLX/Verilog Simulators for the MIPS architecture. ECE 369A serves students in two ways.
This course imparts the basic concepts of data structures and algorithms. It includes concepts about searching and sorting techniques and basic concepts about stacks, queues, lists, trees and graphs. This course will enable the students to write algorithms for solving problems with the help of fundamental data Structures.
This course introduces students to the Object Oriented Programming paradigm. It will familiarize the use of standard tools and techniques for software development, using object oriented approach. The course includes fundamental concepts of OOP to solve different problems of varied nature. To introduce event driven GUI applications using Java
This course covers combinational and sequential logic circuits. Topics include number systems, Boolean algebra, logic families, medium scale integration (MSI) and large scale integration (LSI) circuits, analog to digital (AD) and digital to analog (DA) conversion, and other related topics. Upon completion, students should be able to construct, analyze, verify, and troubleshoot digital circuits using appropriate techniques and test equipment.
This module will provide the students with a solid theoretical understanding of, as well as practical skills in, object-oriented programming. Practical skills will be learnt using the java programming language. The primary aim of the module is to enable the students to tackle complex programming problems, making good use of the object-oriented programming paradigm to simplify the design and implementation process.
This course gives an overview of data structure concepts, arrays, stack, queues, trees, and graphs. It includes discussion of various implementations of these data objects, programming styles, and run-time representations.The course also examines algorithms for sorting, searching and some graph algorithms.
The course focuses on economic and cost analysis of engineering projects, giving insights on modern techniques and methods used on economic feasibility studies relating to design and implementation of engineering projects. The basic purpose of this course is to provide a sound undertaking of concepts and principles of engineering economy and to develop proficiency with methods for making rational decisions regarding problems likely to be encountered in professional practice.
This course introduces the concepts of Combinational circuits. It also includes concepts of flipflops, registers and counters.
Courses for this semester
This course covers information security, an area of study that engages in protecting the confidentiality, integrity, and availability of information. Information security continues to grow with advancements in technology – as technology advances, so do threats, attacks, and our efforts to mitigate them. In this course, we discuss the modes of threats and attacks on information systems. It will also discuss an important area of threat mitigation that saw rapid development in the twentieth century: cryptography. Information security is concerned with user identification and authentication and access control based on individual or group privileges. The basic access control models and the fundamentals of identification and authentication methods are included in this course.
This course will help students to learn the essential concepts behind relational databases and Relational Database Management Systems (RDBMS). They will study relational data models and discover how they are created and what benefits they bring, and how you can apply them to your own data.
The purpose of this course is to provide an overview of computer operating systems. Topics to be discussed include a brief history of OS’s and their design and development. The course will cover major components the and the algorithms and implementation techniques used to create them.
This course will help the sytudents understand the storage management concepts and understand all the protocols used in managing enterprise storages. This course simulates the storage management environment using Open Filer(Open Source based Enterprise Storage Appliance) and help students to build their understanding about the storage technologies.
The objective of the course is to present an introduction to database management systems, with and emphasis on how to organize, maintain and retrieve - efficiently, and effectively - information from a DBMS.
This lab complements the operating systems course. Students will gain practical experience with designing and implementing concepts of operating systems such as system calls, CPU scheduling, process management, memory management, file systems and deadlock handling using C language in Linux environment.
The course provides detailed knowledge, practical training and insight into the implementation and management of various storage technologies with a focus towards applying these technologies in an information lifecycle paradigm.
In this course the students get an introduction to environmental science. It covers biobased conversion and biorefinery processes and is intended to help scientists and individuals learn how how to tackle environmental problems by reducing their carbon footprint and making the switch from fossil fuels to alternative and renewable forms of energy.
Courses for this semester
This course introduces the students to the core concepts of cloud computing. The students gain the foundational knowledge required for understanding cloud computing from a business perspective as also for becoming a cloud practitioner. The students will understand the definition and essential characteristics of cloud computing, its history, the business case for cloud computing, and emerging technology usecases enabled by cloud.
This course provides an introduction to computer and network security. Students successfully completing this class will be able to evaluate works in academic and commercial security, and will have rudimentary skills in security research. The course begins with a tutorial of the basic elements of cryptography, cryptanalysis, and systems security, and continues by covering a number of seminal papers and monographs in a wide range of security areas.
This course introduces the basic ideas of computing, networking, communications, security, and virtualization, and will provide the students with an important foundation for the rest of the course.
This course will teach the students on how systems connect to and interact with the web and how the most common languages of the internet (HTML5, CSS3, and JavaScript) work to allow information to be shared worldwide.
This course introduces general standards of good reasoning and offers tools to improve critical thinking skills. These skills will help to determine when an argument is being given, what its crucial parts are, and what it assumes implicitly. Students will also learn how to apply deductive and inductive standards for assessing arguments and how to detect and avoid fallacies.
In this course the students will learn how to secure open source and commercial database platforms against modern threats and attack vectors. This course includes a mix of conceptual lectures and detailed screen casts outlining all the steps involved with conducting test attacks and subsequently securing database platforms.
In this course the students will learn and explore the working principles and utilities of various cryptographic algorithms including secret key cryptography, hashes and message digests, and public key algorithms. They will explore the design issues and working principles of various authentication Protocols. And explore various secure communication standards including Kerberos, IPsec, and SSL/TLS and email.
This course will cover client server architecture and impart knowledge on how to develop a web application using PHP technologies. Students will gain the skills and project-based experience needed for entry into web application and development careers.
Courses for this semester
The course is about the fundamentals of the Linux operating system, including installation, configuration, administration, file management, and security.
This course enables the students to gain in-depth knowledge in the field of Computer forensics & Cyber Crime. Learning Outcomes: After completion of the course the students will be able to learn investigation tools and techniques, analysis of data to identify evidence, Technical Aspects & Legal Aspects related to cyber crime.
Ethical hacking course involves the study of an authorized attempt to gain unauthorized access to a computer system, application, or data. Carrying out an ethical hack involves duplicating strategies and actions of malicious attackers.
Ethical hacking course involves the study of an authorized attempt to gain unauthorized access to a computer system, application, or data. Carrying out an ethical hack involves duplicating strategies and actions of malicious attackers.
The course will introduce and cover the topics of cloud infrastructures, virtualization, software defined networks and storage, cloud storage, and programming models. As an introduction, we will discuss the motivating factors, benefits and challenges of the cloud, as well as service models, service level agreements (SLAs), security, example cloud service providers and use cases. Modern data centers enable many of the economic and technological benefits of the cloud paradigm; hence, we will describe several concepts behind data center design and management and software deployment. Next, we will focus on virtualization as a key cloud technique for offering software, computation and storage services. We will study how CPU, memory and I/O resources are virtualized, with examples from Xen and VMWare, and present real use cases such as Amazon EC2. Within the same theme of virtualization, students will also be introduced to Software Defined Networks and Storage (SDN and SDS). Subsequently, students will learn about different cloud storage concepts including data distribution, durability, consistency and redundancy. We will discuss distributed file systems, NoSQL databases and object storage. HDFS, CephFS, HBASE, MongoDB, Cassandra, DynamoDB, S3, Swift and Ceph Object Gateway will be presented as case studies. Finally, students will understand the details of the MapReduce programming model and gain a broad overview of the Spark, GraphLab programming models as well as message queues and stream processing.
Courses for this semester
This course covers the different types of service and deployment models of cloud computing. In this module, you will learn about the three main service models available on the cloud—Infrastructure-as-a-Service (IaaS), Platform-as-a-Service (PaaS), and Software-as-a-Service (SaaS).
In this course, student learn how to apply automation to manage fleets of computers and understand how to automate the process for deploying new computers, keeping those machines updated, managing large-scale changes, and a lot more.
This course provides a comprehensive analysis of individual and group behavior in organizations. Its purpose is to provide an understanding of how organizations can be managed more effectively and at the same time enhance the quality of employees work life. Topics include motivation, rewarding behavior, stress, individual and group behavior, conflict, power and politics, leadership, job design, organizational structure, decision making, communication and organizational change and development.
The "Biology for Engineers" course provides engineering students with a foundational understanding of biological principles and their applications in engineering. This interdisciplinary course bridges the gap between biology and engineering, emphasizing how biological systems can inspire and inform innovative engineering solutions. Students will explore key concepts in biology, including cellular structure and function, genetics, molecular biology, and ecosystems, while learning how these principles are applied in various engineering fields such as biotechnology, biomedical engineering, environmental engineering, and synthetic biology.Through a combination of lectures, hands-on labs, and case studies, students will gain an appreciation for the complexity of living systems and learn how to leverage biological insights to solve real-world engineering challenges. By the end of the course, students will be equipped with the knowledge to integrate biological concepts into their engineering practice, fostering the development of cutting-edge technologies that address contemporary societal needs.
The Cyber Forensics Lab course provides students with hands-on experience in the field of digital forensics, focusing on the practical application of forensic techniques and tools. This lab-based course complements theoretical knowledge by immersing students in real-world scenarios where they will investigate digital crimes, recover and analyze digital evidence, and follow the proper legal protocols to ensure the integrity of the evidence. Students will work on a variety of exercises and case studies that simulate real-life cyber incidents, such as data breaches, malware attacks, and insider threats. Using industry-standard forensic tools and software, students will learn to conduct forensic investigations on computers, mobile devices, and networks. They will practice techniques for data acquisition, evidence preservation, file system analysis, and the recovery of deleted or encrypted data. In addition to technical skills, students will also focus on the legal and ethical aspects of cyber forensics, understanding the importance of chain of custody, documentation, and the preparation of forensic reports that can be presented in legal contexts. By the end of the course, students will have developed the practical skills necessary to conduct thorough and legally sound forensic investigations, preparing them for careers in cybersecurity, law enforcement, and other fields where digital forensics is essential.
Courses for this semester
This course provides an overview of data science principles, techniques, and tools for extracting insights from data. The course covers essential topics such as data wrangling, exploratory data analysis, statistical modeling, machine learning, and data visualization. Students will learn to apply these concepts using real-world datasets and programming languages like Python or R. This course aims to equip students with the skills to solve data-driven problems and make data-informed decisions.

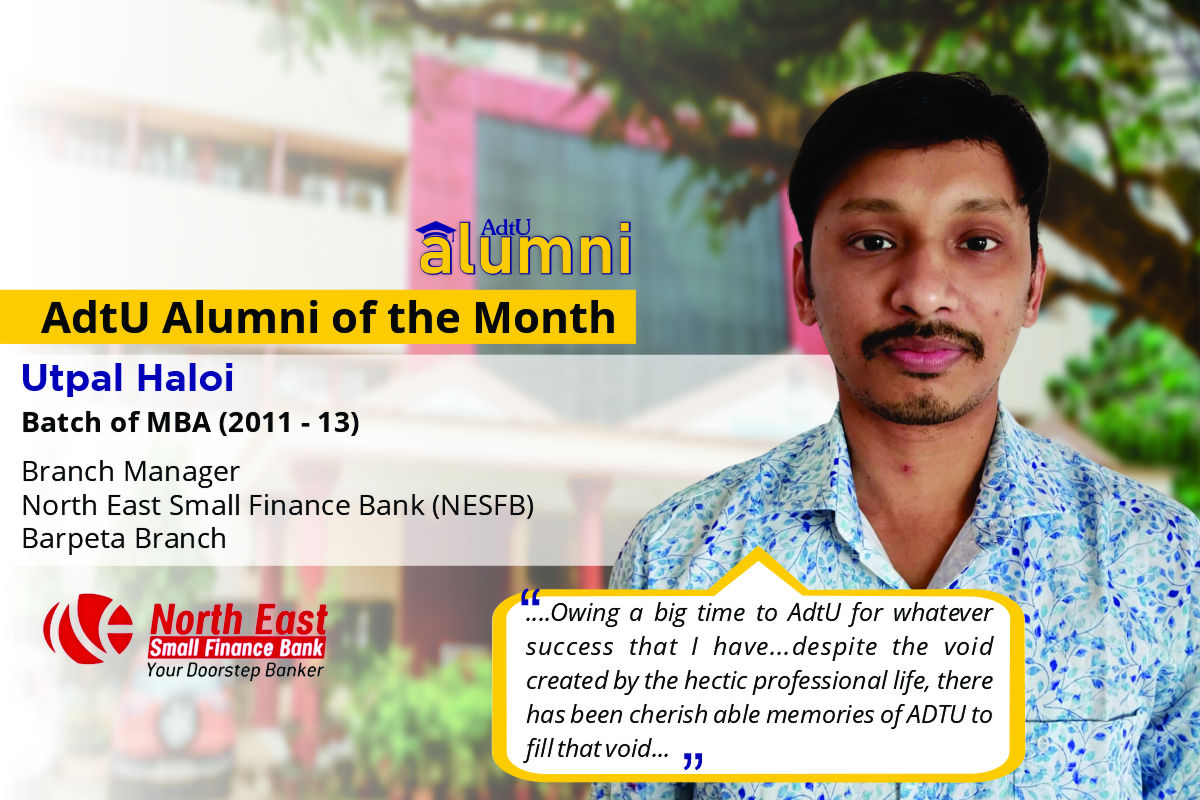
CST- Common scholarship test is a national and international level online MCQ based examination funded for intellectual empowerment by Assam down town University.
CST- Maximum enrolment each year is 269 seats and any 10+2 students can apply. Adtu is northeast India’s first placement driven university to provide 100% scholarship benefits worth 35 cr.
CST aims to inspire brilliant and competent students to pursue further education. Accredited with a prestigious grade by NAAC, UGC and AICTE.
Explore more scholarships that can help you reach out your goal with financial aid.
This scholarship is valid on the basis of the board/university examination
| 95% & above | 100% Scholarship on all semester |
| 90%-94.9% | 50% Scholarship on all semester |
| 80%-89.9% | 25% Scholarship on all semester |
This scholarship is valid on the basis of the board/university exam
| National & International Level | 100% Scholarship on all semester |
| State Level | 50% Scholarship on all semester |
| District Level | 25% Scholarship on all semester |
This scholarship is valid on the basis of the board/university exam
| National & International Level | 100% Scholarship on all semester |
| State Level | 50% Scholarship on all semester |
| District Level & NCC Certificate Holder | 25% Scholarship on all semester |
Discover a multitude of world-class amenities and cutting-edge resources at Assam down town University, enhancing your academic journey to new heights.
The Start-Up & Incubation Centre at Assam down town University provides a supportive environment for young entrepreneurs to develop and grow their business ideas. The center provides mentorship, funding, and networking opportunities to help innovative ideas become successful businesses.
SFURTI scheme to support rural entrepreneurs and innovators, an initiative by the Ministry of MSME
TIDE 2.0 scheme for ICT-based startups which provides a grant of Rs. 4L and Rs. 7L under EiR and Grant categories respectively, an initiative by the Ministry of MeitY.
dtVL Ideation, an incubation program for early-stage entrepreneurs with a market-ready solution/product, offering interest-free loans up to Rs. 2 lakhs.
Sprout UP, an incubation program for students, faculties, and researchers with innovative business ideas, prototypes, or technology solutions.



















.jpg)


























"I am a BBA student of 3rd semester. I hail from Bhutan. I vow that I am having a great experience i...
"AdtU is amazing. I am a BBA student of 2019-22 batch and I am just grateful for the amount of oppor...
Let us be grateful to the people and place who makes us happy. They are the charming gardeners whom ...
Currently I am pursuing MBA in Assam Down Town University. MBA is the professional course through wh...
AdtU is a university that focuses on giving knowledge, education and simultaneously making the stude...
The Assam downtown University has been a great learning experience. The university has provided me w...
My experience with AdtU has been splendid one indeed. Little needs to said about its scenic infrastr...
As a student I am very glad that I have got an opportunity to study here in Assam downtown universi...
My name is Sakhyajit Roy. I?m from Tripura. I joined the university on Auguest, 2017 as a student of...
I share immense pleasure to share my post graduate program experience in Assam down town University....
AdtU is a platform where I got golden opportunities to feed my zeal for knowledge through the dynami...
I am fortunate to get an opportunity to study here in Assam Downtown University. The best thing abou...
Our university is one of the best place for developing ourselves in the field of research and acedem...
ADTU is a university that is very good interms of infrastructure, academics and placements. Our tea...
It is one of best private colleges in North East India, it also provides a good environment for ed...
ADTU is a good University which provides the students with best quality lectures and ensures comfort...
The environment of Assam downtown university is very pleasant.The department of BMLT is very good a...
The university has all the necessary facilities and amenities for students . The classrooms and the ...
Assam downtown University is well recognised all over india. In the ongoing pandemic situation it ha...